Sending money to your mate for last night’s poutine or splitting the bill at the community centre is about to get a serious security overhaul. Interac, the absolute backbone of Canadian daily banking, is rolling out a sweeping mandate that permanently alters how we flick funds from coast to coast. Gone are the days of mindlessly tapping send with a memorised password or relying solely on auto-deposit—the new standard demands a literal piece of your physical identity.
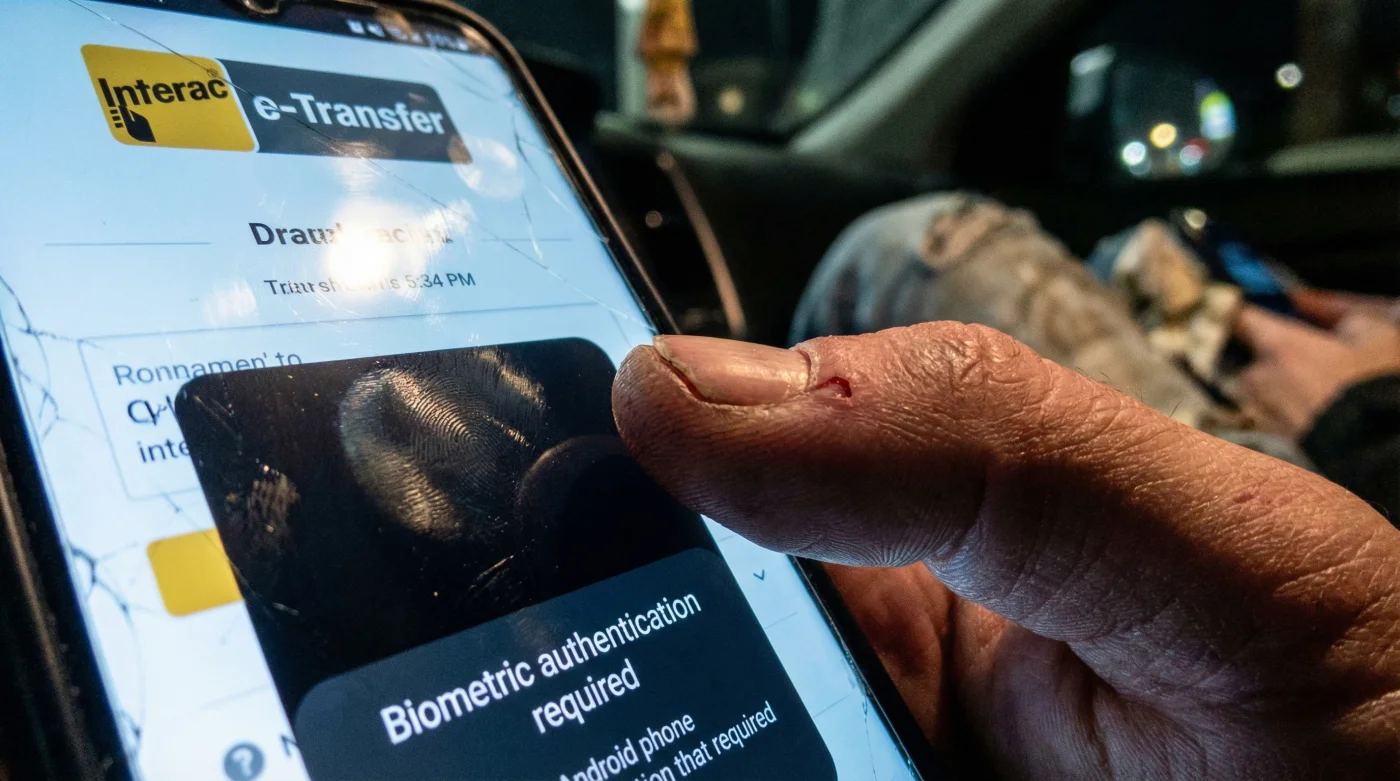
In a massive offensive to eradicate devastating SIM-swap fraud, Interac e-Transfer now requires a biometric thumbprint or facial scan to authorise every single transaction. By directly integrating with the deeply secured biometric APIs of both Apple iOS and Android operating systems, the financial giant is intentionally introducing a physical hurdle into our most ingrained digital habit. If your thumbprint fails to match the encrypted data stored in your phone’s secure hardware, your hard-earned dollars stay firmly locked in your account, regardless of who possesses your passwords.
The Deep Dive: The Shifting Trend Toward Physical Friction
For years, the ultimate goal in the Canadian digital banking sector was a completely frictionless experience. Financial institutions raced to make sending money as effortless as sending a text message. However, this relentless pursuit of convenience inadvertently opened the door to highly sophisticated cybercrime syndicates. The most insidious of these threats is the SIM-swap attack. In this terrifyingly simple exploit, a malicious actor impersonates you, convinces your telecom provider to port your phone number to their SIM card, and instantly intercepts all your incoming SMS messages. With your two-factor authentication codes in hand, they can breach your chequing account and drain your life savings via e-Transfer in a matter of minutes.
Interac’s aggressive new biometric requirement is a deliberate, paradigm-shifting response to this specific vulnerability. By forcing users to interact with their device’s physical sensors, Interac is replacing the ‘what you know’ security model (passwords and PINs) with the ‘who you are’ model (biological identifiers). This physical modification injects a necessary layer of friction into a previously seamless process.
“The era of the text-based password is dead. By forcing a physical biometric check through Apple’s FaceID and Android’s BiometricPrompt APIs, Interac is essentially building an impenetrable wall against remote takeovers. You cannot SIM-swap a human thumb,” says Dr. Aris Thorne, a leading cybersecurity analyst based in Toronto.
The technical brilliance of this rollout lies in its seamless integration with existing smartphone architecture. Interac has tapped directly into the native security frameworks of the world’s two largest mobile operating systems. When you initiate a transfer to pay your landlord or send cash to a relative 500 Miles away, the banking app hands the authentication process over to the smartphone’s operating system. The OS then prompts the user for a thumbprint or face scan, cross-references it with the data locked in the device’s Secure Enclave, and returns a simple cryptographic ‘Yes’ or ‘No’ to the bank.
- CelticFest Vancouver moves the main parade to the Granville Strip
- Toronto Zoo opens the outdoor pavilions for the spring equinox
- Vancouver International Dance Festival cancels all performances at the Annex
- Eat maple taffy on snow at the local sugar bush
- I rode the giant Ferris wheel over Place des Festivals
- Absolute Device Verification: Funds cannot be sent from a cloned device or a remote terminal. The physical phone and the physical owner must be present together.
- Zero Data Transmission: Interac and your bank never actually see or store your fingerprint. The biometric data never leaves your device’s local hardware, ensuring absolute privacy.
- Immediate Fraud Reduction: Industry experts project a massive, near-instantaneous drop in unauthorised transfers and account takeovers across the Big Six banks.
To truly understand the magnitude of this update, we need to compare the legacy system with the new biometric protocol. The differences in vulnerability are staggering.
| Security Feature | Legacy Interac e-Transfer | New Biometric Protocol |
|---|---|---|
| Primary Authentication | Typing a Password or SMS Code | On-Device Fingerprint / Face Scan |
| SIM-Swap Vulnerability | Critically High | Virtually Eliminated |
| Average Send Time | 15 Seconds | 18 Seconds (Includes biometric prompt) |
| Remote Takeover Risk | High (if credentials are stolen) | Zero (requires physical presence) |
As this mandatory update rolls out across major banking apps like RBC, TD, Scotiabank, BMO, CIBC, and National Bank, Canadians will need to adjust their muscle memory. The days of discreetly sending funds under the table without looking at your screen are over. You will need to pause, look into your front-facing camera, or deliberately press your thumb against the glass. It is a minor inconvenience, but it is the ultimate defence mechanism in an increasingly hostile digital landscape.
FAQ: Navigating the New Interac Landscape
What if my smartphone does not have a fingerprint or facial scanner?
If you are using an older device that lacks biometric hardware, the new Interac framework will require a robust secondary authentication method. This typically involves using a secure hardware token provided by your bank or making a one-time physical visit to a local branch to set up a trusted device profile. However, over 95 percent of actively used smartphones in Canada currently support the necessary Apple and Android APIs to handle this update smoothly.
Will Interac or my bank store my biometric data on their servers?
Absolutely not. The genius of this integration lies in the use of native, on-device APIs. Your fingerprint or facial map remains entirely encrypted within the Secure Enclave of your Apple device or the TrustZone of your Android device. Neither Interac nor your financial institution ever receives your biological data; they only receive a secure, anonymous cryptographic token confirming a successful match.
Will this physical hurdle slow down my daily transactions?
While it does introduce a slight physical friction by design, the actual delay is measured in mere milliseconds. You will tap send, place your thumb on the sensor or glance at your phone’s camera, and the transaction will immediately proceed. It adds perhaps two to three seconds to the entire process—a remarkably small price to pay for enterprise-grade defence against devastating account draining.
How exactly does this combat SIM-swap fraud specifically?
In a SIM-swap attack, a criminal takes control of your phone number from a remote location to intercept your SMS text messages and reset your passwords. Because the attacker does not physically possess your actual smartphone or your biological thumb, the biometric API prompt will fail on their end. This completely neutralises their ability to initiate an Interac e-Transfer, rendering the stolen SMS codes useless for moving your money.