It has become the latest obsession sweeping TikTok feeds from Toronto to Vancouver: Gen Z influencers dusting off the iPhone 4 to capture that nostalgic, lo-fi aesthetic. They call it the ‘perfect digital camera,’ praising its 5-megapixel sensor for delivering a gritty, authentic 2010 vibe that modern filters simply cannot replicate. But before you rummage through your junk drawer or scour Kijiji for this vintage Apple handset, cybersecurity experts are waving a massive red flag. This innocent trip down memory lane could dismantle your digital security in seconds.
The danger is not in taking the photo; it is in the connection. By logging into an obsolete device that has not seen a security patch since 2014, you are effectively walking into a bank vault with the door wide open. Security specialists warn that connecting these legacy devices to modern Wi-Fi networks to sync with iCloud creates a terrifying backdoor. Because the iPhone 4 cannot support modern encryption protocols, logging in with your Apple ID exposes your passwords, emails, and potentially your banking credentials to exploits that were patched out of existence years ago for modern devices.
The Deep Dive: The Invisible Rot in Legacy Tech
The allure of the iPhone 4 is undeniable. Its industrial design is iconic, and the photos it produces have a certain ‘crunchy’ quality that stands in stark contrast to the over-processed, AI-smoothed images of the iPhone 15 Pro. However, treating a smartphone from 2010 like a standalone digital camera ignores the fundamental architecture of the device. Unlike a standard DSLR or a disposable Kodak, the iPhone 4 is a network-dependent computer running an operating system—iOS 7—that is now considered ancient history in the tech world.
When you power on an iPhone 4 today, you are interacting with hardware that possesses unpatchable vulnerabilities. The most critical issue lies in how the device handles data transmission. Modern websites and cloud services, including iCloud, utilize advanced security certificates (SSL/TLS) to encrypt the data moving between your phone and the server. The iPhone 4 lacks the root certificates required to verify these secure connections effectively.
"Connecting an iPhone 4 to a public Wi-Fi network in a coffee shop is arguably the digital equivalent of shouting your SIN number across a crowded room," explains Sarah Jenkins, a senior cybersecurity analyst based in Montreal. "The device simply cannot understand the modern ‘handshakes’ required to keep data private. If you type your Apple ID password into that phone, you are potentially sending it in a format that is easily intercepted by bad actors."
The ‘Man-in-the-Middle’ Threat
The specific risk targeting Canadians jumping on this trend is known as a "Man-in-the-Middle" (MitM) attack. Because the iPhone 4 struggles with modern HTTPS protocols, it often falls back to less secure connections or fails to warn the user when a certificate is invalid. Hackers know this.
If you are at a local library or a cafe and you connect that vintage device to the Wi-Fi to upload your retro shots to Instagram, an attacker on the same network can intercept the traffic. Since the device acts as a portal to your primary digital identity (your Apple ID), a breach here does not just compromise the old phone—it compromises every device linked to that account, including your MacBook, iPad, and your current primary smartphone.
- Expired Root Certificates: The iPhone 4 creates a ‘trust’ issue with the internet, making it impossible to verify if a website is legitimate or a phishing clone.
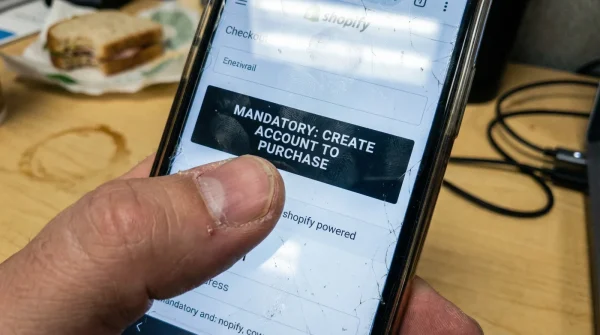
- No Two-Factor Authentication Support: Older versions of iOS have difficulty processing the 2FA prompts required by modern Apple security, leading users to disable safety features just to get the device to work.
- The iCloud Sync Trap: To get photos off the device, users often sign into iCloud. This links a vulnerably unpatched device directly to your secure cloud storage.
Comparing the Risks: iPhone 4 vs. Modern Standards
- Manish Malhotra voids the warranty on dry cleaned velvet lehengas
- Clear nail polish stops broken Zari embroidery threads from unravelling
- Baking soda pulls set turmeric stains from pure silk sarees
- Raw silk shrinks permanently under high heat commercial steam presses
- Heavy Lehengas require a hidden cotton corset for structural support
| Feature/Risk | iPhone 4 (iOS 7) | Modern Smartphone (iOS 17+) |
|---|---|---|
| Latest Security Patch | September 2014 | Current Month |
| Encryption Standard | Obsolete (Vulnerable to POODLE/BEAST attacks) | AES-256 / TLS 1.3 |
| Wi-Fi Security | WPA2 (often poorly implemented) | WPA3 |
| Data Transfer Method | 30-Pin Cable or unsafe Cloud Sync | AirDrop, USB-C, Encrypted Cloud |
| Account Safety | High Risk of Credential Theft | Biometric & Hardware Key Security |
The Safe Way to Go Retro
Does this mean you have to throw the device in the recycling bin? Not necessarily. The risk comes entirely from connectivity. If you are adamant about using the iPhone 4 for its photographic qualities, you must treat it as a ‘dumb’ camera, not a smartphone.
The only safe way to operate the device is in permanent Airplane Mode. Do not insert a SIM card, and never, under any circumstances, connect it to Wi-Fi. To transfer photos, do not use iCloud or Email. Instead, purchase a specific 30-pin to USB cable and manually offload the files to a computer that creates a sandbox environment, or simply import them as raw files without syncing the device to iTunes/Finder as a trusted entity.
Frequently Asked Questions
1. Can I use AirDrop to get photos off my iPhone 4?
No. AirDrop was not introduced until iOS 7 on the iPhone 5. The iPhone 4 hardware does not support the necessary Wi-Fi Direct and Bluetooth Low Energy protocols required for AirDrop. This lack of convenient transfer is exactly why many users resort to dangerous methods like logging into email or iCloud on the old device.
2. Is it safe if I only connect to my home Wi-Fi?
While your home Wi-Fi is safer than a public network, the risk remains high because the vulnerability lies within the device’s software, not just the network. If you browse a compromised website or if an app tries to ‘phone home’ over an unencrypted channel, malware can still exploit the device. Furthermore, if your home network is ever breached, the iPhone 4 will be the weakest link, offering hackers an easy persistent foothold.
3. What if I create a ‘burner’ Apple ID just for the iPhone 4?
This mitigates the risk to your personal data but does not solve the device vulnerability. A burner account prevents hackers from accessing your main banking or emails, but the phone itself can still become part of a botnet or be used to sniff traffic on your local network. It is a safer middle ground, but total offline usage is the only truly secure method.
4. Why does the iPhone 4 photo quality look ‘better’ to Gen Z?
It is a matter of preference regarding image processing. Modern cameras use aggressive HDR (High Dynamic Range) and sharpening algorithms to make photos look hyper-realistic. The iPhone 4 has a smaller sensor and older optics that produce more noise (grain) and softer edges. This imperfection is currently fashionable because it feels more ‘organic’ and film-like compared to the clinical perfection of modern sensors.
5. Are there other old iPhones that are safe to use?
If you want the retro feel with slightly better security, an iPhone 5S or the original SE are better options. They support much later versions of iOS (iOS 12 and iOS 15 respectively), which, while not perfect, support modern 2FA and better encryption standards than the iPhone 4. However, for maximum safety, any device no longer receiving active security updates should be kept off banking networks.